Event Planning
Multi-Chain Identity Verification for Events
DIDs, Verifiable Credentials and cross-chain protocols use zero-knowledge proofs to privately verify event attendees, prevent fraud, and speed entry.


February 2nd, 2026
•
14 min read
Multi-Chain Identity Verification for Events
Event organizers often face the challenge of verifying attendees' identities without risking their privacy. Multi-chain identity verification offers a decentralized solution, using Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs) across blockchains like Ethereum, Solana, and Polkadot. This approach ensures secure identity checks without relying on centralized systems, making events safer and more efficient.
Key Benefits:
- Privacy: Attendees can prove eligibility (e.g., age, VIP status) using Zero-Knowledge Proofs without revealing personal data.
- Security: Eliminates centralized databases, reducing the risk of breaches.
- Interoperability: Credentials work across multiple blockchains, simplifying access for global events.
- Efficiency: Cryptographic verification speeds up entry, reduces manual work, and prevents fraud like ticket duplication or bot access.
How It Works:
- DIDs: Unique, user-controlled identifiers verified via cryptographic signatures.
- VCs: Digital credentials (like tickets) stored in wallets, tamper-proof and instantly verifiable.
- Cross-Chain Protocols: Enable seamless use of credentials across different blockchain ecosystems.
This system combats challenges like bots, ensures privacy compliance, and reduces operational costs, making it a game-changer for event management.
The Future of Identity: On-chain Identity
How Multi-Chain Identity Verification Works in Events
Multi-chain identity verification simplifies how attendees prove their identity and access rights at events. At its core, it uses two key components: Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs). Together, these tools ensure a secure and efficient process while safeguarding personal information. Let’s dive into how they work.
Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs)
A Decentralized Identifier (DID) is like a digital passport that works across blockchains. Unlike traditional usernames tied to specific platforms, DIDs are globally unique and controlled entirely by the individual - no central authority is involved. Ownership is verified through cryptographic signatures, adding an extra layer of security.
Verifiable Credentials (VCs), on the other hand, act as digital versions of physical documents like tickets or ID cards. What sets them apart is their tamper-proof design. According to the W3C Verifiable Credentials Working Group:
"A verifiable credential can represent all the same information that a physical credential represents. Adding technologies such as digital signatures can make verifiable credentials more tamper-evident and trustworthy than their physical counterparts."
The process relies on three roles: an Issuer who creates the credential, a Holder who stores it, and a Verifier who confirms its authenticity. This setup eliminates the need for Verifiers to contact the original Issuer, allowing fast and scalable verification.
Cross-Chain Protocols for Identity Verification
DIDs and VCs provide a secure foundation, but cross-chain protocols take it a step further by enabling seamless identity verification across multiple blockchains. Instead of managing separate identities for events on Ethereum, Polygon, or other platforms, users verify their identity once and use it everywhere. This is especially important in light of the fact that over 52% of data breaches in 2023 involved customer data stored in centralized systems, with an average cost of $4.45 million per breach.
At the heart of this system are Universal Verifiers - smart contracts that process Zero-Knowledge proofs and data from various chains. These verifiers act as translators, enabling credentials issued on one blockchain (e.g., Ethereum) to be recognized on another (e.g., Polygon) without duplicating data.
Evin McMullen, Co-founder and Chief Strategy Officer at Privado ID, explained:
"We're taking a major leap towards solving the challenge of fragmented identities in the blockchain space... we make it easier to prove things about yourself and unlock value anywhere, in a secure, discreet manner."
Verification times typically range from 2 to 3 minutes as messages are relayed between chains. To keep attendees informed during this process, visual indicators like "Transaction Sent", "Message Relaying", and "Confirmed" are often used.
Event Use Cases: Ticketing, Access Control, and Privacy
By applying these technologies, event management becomes more secure, efficient, and fraud-resistant.
- Digital ticketing: Tickets issued as VCs are cryptographically tied to your DID, making them immune to tampering or duplication. This ensures secure verification at scale, which is critical as global online marketplaces generated over $3.8 trillion in 2024 .
- Automated access control: Presenting your credential at the gate triggers a Universal Verifier smart contract to check your Zero-Knowledge proof. Access is granted instantly, or an entry badge is minted. The use of "nullifiers" (anonymous, single-use identifiers) prevents duplicate entries without tracking your movements .
- Privacy protection: Selective disclosure allows you to prove specific attributes without revealing unnecessary personal details. For instance, you can confirm you're over 21 without sharing your birth date or full name . This approach also supports "unlinkable disclosure", meaning you can verify access without creating a permanent trail across venues .
| Component | Role in Event Management | Key Benefit |
|---|---|---|
| DID | Unique attendee identifier | Works across all blockchains without central control |
| VC | Digital ticket or proof of age | Tamper-proof and instantly verifiable |
| ZKP | Privacy-preserving verification | Proves attributes without exposing personal data |
| Cross-Chain Protocol | Multi-event access | A single identity usable across platforms |
Benefits of Multi-Chain Identity Verification for Event Management
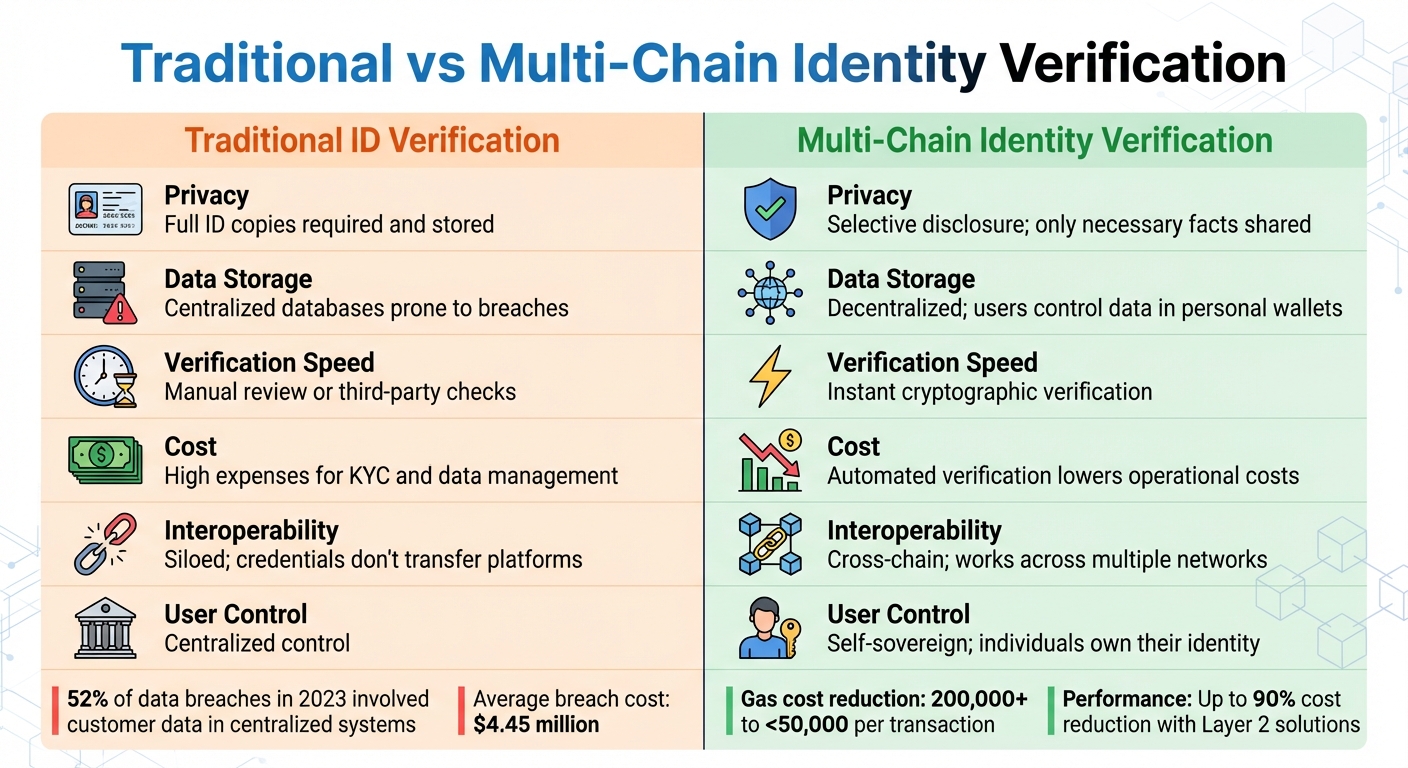
Traditional vs Multi-Chain Identity Verification for Events
By leveraging Decentralized Identifiers (DIDs), Verifiable Credentials (VCs), and cross-chain protocols, multi-chain identity verification brings several advantages to event management:
Better Privacy and Security
Traditional event systems often require attendees to share full ID documents for tasks as simple as age verification. Multi-chain verification changes this process through selective disclosure, allowing attendees to confirm specific details - like being over 21 - without revealing any extra personal information.
Decentralized storage also removes the need for centralized databases, which are vulnerable to breaches. As explained on ethereum.org:
"Decentralized identity removes reliance on centralized third parties. Thanks to crypto, users now have the tools to issue, hold and control their own identifiers and attestations once again."
Zero-Knowledge Proofs (ZKPs) add another layer of security. For example, attendees can prove they possess a valid VIP ticket or alumni credential without exposing the underlying data. These credentials stay in their digital wallets, and event organizers verify their authenticity using cryptographic methods - eliminating the need to store copies of sensitive documents.
Interoperability and Scalability
Cross-chain protocols simplify identity management by enabling credentials issued on one blockchain (like Ethereum) to work seamlessly on others, such as Polygon. This eliminates the need for attendees to manage multiple identities across different platforms, which is especially useful for global events spanning multiple blockchain ecosystems.
For event organizers, this means less administrative work. Smart contracts automate the verification process, reducing costs tied to manual reviews and database upkeep. Attendees also enjoy a smoother experience - one digital wallet, one identity, and easy access to events, regardless of the blockchain in use.
These streamlined processes highlight the practical advantages of multi-chain identity verification when compared to traditional methods.
Traditional ID Verification vs. Multi-Chain Verification
Multi-chain identity verification addresses the limitations of conventional systems by leveraging decentralization. Here's a side-by-side comparison:
| Feature | Traditional ID Verification | Multi-Chain Identity Verification |
|---|---|---|
| Privacy | Full ID copies required and stored | Selective disclosure; only necessary facts shared |
| Data Storage | Centralized databases prone to breaches | Decentralized; users control data in personal wallets |
| Verification Speed | Manual review or third-party checks | Instant cryptographic verification |
| Cost | High expenses for KYC and data management | Automated verification lowers operational costs |
| Interoperability | Siloed; credentials don't transfer platforms | Cross-chain; works across multiple networks |
| User Control | Centralized control | Self-sovereign; individuals own their identity |
Moreover, technological advancements like the Oracle Blockchain Platform show a 2× improvement in read performance compared to older systems like Hyperledger Indy. Tools such as Bitstring Status Lists enable efficient credential checks at scale, while CBOR formatting minimizes data size, making it easy to share credentials via QR codes for quick event entry.
sbb-itb-8eb1bfa
Implementing Multi-Chain Identity Verification on Zenao
Setting Up DIDs and VCs in Zenao
To get started with identity verification on Zenao, it's important to understand Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs). A DID acts as a unique identifier that doesn’t rely on a central authority. As the Veramo Documentation explains:
"A DID is a new type of unique identifier which can be created independent of a central authority. The subject that the DID refers to can prove control over the DID using cryptographic proofs."
Each DID is linked to a DID Document, which contains public keys and service endpoints. This allows users to prove ownership of their identity using cryptographic methods. Depending on your system, you can choose did:web for web-based identities or did:ethr for Ethereum-based systems.
When issuing credentials like event tickets or VIP badges, event organizers act as issuers, signing and distributing VCs to attendees (the holders). These credentials contain metadata such as the issuer's identity, expiration date, and specific claims about the holder, all backed by digital proof. The Privado ID Documentation highlights the benefits of using blockchain for this process:
"The fact that all this logic is present on the blockchain enables credential issuance for DAOs in a programmatic way. It can also be useful for entities like oracles and on-chain analytics companies since the contract code can be audited and verified."
To save on costs, store only the IPFS hash of a DID document on the blockchain instead of the full JSON. This reduces gas usage from over 200,000 gas to under 50,000 gas per transaction. Using JSON Schemas ensures that all issued credentials follow a consistent format, making them easier for third-party systems to verify.
Once DIDs and VCs are set up, the next step is to integrate cross-chain support for broader verification capabilities.
Enabling Cross-Chain Support and Smart Contracts
To enable cross-chain functionality, Zenao uses a Universal Verifier smart contract. This contract simplifies the validation of Zero-Knowledge (ZK) proofs and cross-chain data, so you don’t have to build verification logic from scratch. Link the Universal Verifier to your event contract and assign unique REQUEST_ID values for each verification query, such as age verification or Proof of Humanity.
Incorporate verification modifiers in your smart contracts. For instance, use verifier.getProofStatus(address, REQUEST_ID).isVerified to automate checks before allowing actions like ticket transfers or granting access. This eliminates manual reviews while maintaining security. For cross-chain operations, Zenao employs CAIP identifiers (chain, asset, account) to ensure identities function seamlessly across networks like Ethereum, Polygon, and Bitcoin.
The verification process involves gathering User State and Issuer State from the original chains where credentials were issued. A Resolver service then signs these states. Attendees generate a ZK proof based on their VC and signed states, submitting it to the verification chain using the submitZKPResponseV2 method. For added security, consider configuring an operator quorum that requires multiple trusted signatures before confirming cross-chain identity claims. Monitor Cross-Chain Interoperability Messages (CCIM) to prevent replay attacks on credentials.
After setting up cross-chain support, focus on testing and refining the system to ensure smooth operations during events.
Testing and Optimizing for Events
Testing is critical to ensure reliability. Use testnets like Sepolia or Amoy to validate your contracts. Confirm that the "Source-Transport-Destination" model works as expected - this means a smart contract on Chain A should emit a message that gets correctly decoded and executed by a contract on Chain B.
For performance, decide between on-chain stateful verification and off-chain static verification with local caching. Off-chain caching can significantly speed up DID resolution by refreshing only when a DIDUpdated event occurs, achieving sub-second response times. For high-traffic events, peer-to-peer credential sharing via WebRTC can reduce network congestion and minimize unnecessary blockchain reads during check-ins.
Batching DID operations and leveraging Layer 2 solutions can cut gas costs by up to 90%. Before initiating destination-chain activities like badge minting or access control, keep an eye on your operator quorum status for cross-chain actions. Zero-Knowledge Proofs allow for Selective Disclosure, enabling attendees to verify specific criteria (like age or membership) without exposing private data - this is key for balancing privacy and compliance.
Challenges and Compliance Strategies
Interoperability and Technical Issues
One of the toughest nuts to crack in blockchain technology is getting different networks to play nicely together. Each blockchain has its own way of reaching consensus - like Ethereum's Proof-of-Stake, Bitcoin's Proof-of-Work, or Raft used in some private chains. These differences make it tricky to synchronize transactions or share data seamlessly. On top of that, the scripting capabilities vary widely. For instance, Bitcoin's scripting is basic, while Ethereum offers full-fledged smart contract functionality through Solidity. This mismatch creates hurdles when trying to share automated logic across platforms.
A smart way to tackle these challenges is by using modular architectures built on universal standards. Tools like W3C Verifiable Credentials and Decentralized Identifiers provide a machine-readable format that works across different blockchain ecosystems . Another effective strategy is to keep sensitive business data on private blockchains while using interchain protocols to anchor security proofs on public blockchains.
A good example of this in action comes from Dragonchain. In January 2020, they ran a live test, processing over 250 million transactions in 24 hours with an average throughput of 2,800 transactions per second (TPS), peaking at 15,000 TPS. This kind of performance shows that addressing interoperability challenges is not just possible but necessary for meeting privacy regulations and Know Your Customer (KYC) requirements.
Privacy Regulations and KYC Requirements
When it comes to privacy and compliance, decentralized verification offers a promising path forward. However, meeting regulations like GDPR and CCPA requires innovative off-chain solutions. Traditional KYC systems have proven risky - just think back to the 2017 Equifax breach, which exposed the personal data of 147 million people. By contrast, multi-chain verification shifts the focus to a "proof-of-verification" model. This allows users to confirm they meet criteria like age or residency without revealing their personal data .
To protect privacy, personal information should stay off-chain with trusted KYC providers. Only a cryptographic attestation - essentially a secure proof - is stored on the blockchain. Using techniques like selective disclosure, users can prove they're over 18 without sharing their exact birthdate. Event smart contracts can then use a registry contract to map wallet addresses to verification flags, ensuring attendees meet access requirements before granting entry.
This isn’t just theoretical - it’s happening now. In October 2025, Bhutan moved its National Digital Identity system to the Ethereum mainnet. Over 234,000 digital IDs were issued, allowing 800,000 citizens to verify their citizenship or age using zero-knowledge proofs, all without exposing personal details. Similarly, Buenos Aires integrated the QuarkID protocol into its "miBA" app on ZKSync Era Layer 2 in 2024. This enabled 3.6 million users to share documents like birth and marriage certificates peer-to-peer while maintaining privacy.
For event organizers, there are a few best practices to follow. Refresh sanctions lists daily for high-stakes events and set up recovery options for users who lose their cryptographic keys. Tools like zk-SNARKs, which generate compact proofs of around 200 bytes, can also help reduce gas costs. As Chainscore Labs puts it:
"The goal is to meet legal compliance requirements without compromising the core principles of user privacy and self-sovereignty inherent to Web3."
Considering that financial institutions spend up to $500 million annually on KYC/AML compliance, multi-chain identity verification could slash these costs while improving privacy and user experience.
Conclusion: The Future of Identity Verification in Events
Multi-chain identity verification is reshaping how events handle security, privacy, and accessibility. By moving away from centralized identity databases, event organizers empower attendees with direct control over their data while staying compliant with regulations. This shift - from repeatedly verifying identities for each service to using reusable, cross-chain credentials - removes unnecessary hurdles, creating a smoother experience across blockchain ecosystems like Ethereum, Polygon, and Solana.
This isn't just a concept; it's already happening. Global case studies highlight how privacy-focused verification at scale is being implemented today. These examples show the growing demand for flexible, cross-chain solutions in event management.
To meet this demand, event organizers should prioritize interoperability and advanced verification methods. Adopting W3C-compliant Decentralized Identifiers and Verifiable Credentials ensures compatibility across platforms. Established protocols like zero-knowledge proofs (ZKPs) and risk-based workflows can dynamically adjust verification steps in real time. This reduces friction for genuine attendees while maintaining strong defenses against Sybil attacks and ticket scalping.
Zenao is at the forefront of this transformation, providing a decentralized platform that integrates multi-chain identity verification into event management tools. With features like digital ticketing, community governance, and upcoming ZKP support for private events, Zenao allows organizers to implement sophisticated verification without requiring technical expertise. Its no-code approach enables rapid adaptation to changing privacy laws and event needs, cutting implementation times from months to days.
As Evin McMullen, Co-founder and Chief Strategy Officer at Privado ID, puts it:
"This protocol is the missing middleware infrastructure that mainstream Web3 ecosystems need to drive value continuously from the infrastructure toward the application layer".
The future of event management is about more than just scanning tickets. It’s about creating secure, scalable, and accessible experiences where attendees retain control of their data, and organizers achieve compliance without sacrificing privacy.
FAQs
How does multi-chain identity verification improve privacy for event attendees?
Multi-chain identity verification takes privacy to the next level by leveraging zero-knowledge proofs (ZKPs). With this cryptographic technique, individuals can confirm specific credentials - like their age or membership status - without revealing personal details such as their full name or date of birth. This minimizes exposure of sensitive data, significantly lowering the chances of breaches or unauthorized access.
Decentralized systems also empower individuals to maintain control of their identity data, aligning with the concept of self-sovereign identity (SSI). This means attendees can choose to share only the verified details necessary for a particular event, keeping the rest of their information private. The result is a secure, privacy-first method for managing identities across multiple events and platforms.
How do Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs) improve event management?
Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs) are reshaping the way identity verification works in event management, making it safer, more private, and easier to use. DIDs are unique digital identifiers that don't rely on a central authority. Instead, they let individuals fully control their identity information. This decentralized setup helps combat issues like fraud and identity theft, which are all too common in event registration and ticketing.
Verifiable Credentials (VCs) complement DIDs by securely managing claims such as event tickets, age verification, or membership details. These credentials can be stored in digital wallets and verified instantly at event check-ins, cutting down on manual processes and eliminating the risk of counterfeit tickets. Together, DIDs and VCs offer a streamlined, privacy-first identity system that's especially useful for organizing everything from workshops to festivals and large-scale events.
How do cross-chain protocols enable secure and seamless identity verification across blockchains?
Cross-chain protocols simplify and secure identity verification across different blockchains by enabling them to work together seamlessly. These protocols use methods like cross-chain messaging and cryptographic signatures to allow blockchains to exchange data and validate credentials. This means users' information can be verified and trusted across networks, even when the blockchains function independently.
Privacy gets an extra layer of protection with zero-knowledge proofs, which let users confirm their identity without exposing sensitive details. When combined with tools like multi-signature validations and other security measures, these technologies create a solid framework for verifying identities in multi-blockchain ecosystems. This makes tasks like event management and community interactions much more straightforward.
