Governance
How Time-Locked Voting Works in Blockchain Systems
How time-locked voting delays proposal execution: queueing, commit-reveal privacy, role-based timelocks, oracle timing, and governance trade-offs.


February 11th, 2026
•
11 min read
How Time-Locked Voting Works in Blockchain Systems
Time-locked voting is a method used in blockchain governance to delay the execution of decisions after a vote. This delay allows community members to review, challenge, or exit before actions are finalized. It operates through smart contracts, ensuring decisions follow a structured timeline: proposals are queued, delayed, and only executed after the waiting period expires. This approach improves security, reduces risks like front-running, and prevents hasty decisions.
Key features include:
- Roles: Proposers queue tasks, Executors finalize them, and Cancellers can abort pending actions.
- Timing: Delays are enforced using Unix timestamps or block height, with minimum delays often set at two days for safety.
- Encryption: Techniques like commit-reveal models and hashing keep votes private during the process.
This system is widely used in DeFi protocols like Uniswap and Compound, offering better control over governance decisions. However, challenges like gas costs and timing reliance on external triggers remain.
Use Cases:
- Community Governance: Managing protocol updates or treasury allocations.
- Event Coordination: Platforms like Zenao.io can use it for scheduling and budgeting.
- Emergency Safeguards: Prevents unilateral administrative changes.
While time-locked voting enhances blockchain decision-making, it requires careful implementation to balance security and efficiency.
Key Components of Time-Locked Voting Mechanisms
Time-locked voting operates on three essential technical elements, each working in harmony to ensure a secure and reliable process. These components safeguard votes until the designated moment for execution.
Role of Smart Contracts
Smart contracts are the backbone of time-locked voting, automating the process and enforcing role-based access control. Specific roles are assigned, such as Proposers, who queue operations; Cancellers, who can halt pending actions; and Executors, who finalize transactions once the timer expires. Through conditional checks like if (block.timestamp < unlockTime), smart contracts ensure no function is executed before the unlock time.
To preserve integrity during the waiting period, these contracts rely on hashing algorithms like keccak256 or Pedersen hashes. These algorithms create unique identifiers for queued transactions, making tampering impossible. Additionally, commit-and-reveal schemes are used to enhance security. Initially, encrypted commitments are collected, and after the lock period ends, the revealed data is verified against the original hash. Some protocols even introduce economic incentives, such as requiring deposits that can be forfeited if a user fails to reveal their vote or submits invalid information.
Blockchain Timing and Synchronization
Accurate timing is critical for managing vote execution. Blockchain timing serves as the clock that determines when votes can be revealed or executed. However, blockchains do not perform actions autonomously, so external triggers like oracles or automation services are necessary to execute functions when the time window opens.
"Many smart contracts on Ethereum require an external source of timing to trigger an on-chain action. For dApps using on-chain blockchain voting systems, this presents a challenge since voting windows are limited to a specific time." - Chainlink
To manage timing effectively, most implementations use three constants: MIN_DELAY (e.g., 1 minute), MAX_DELAY (e.g., 1 hour), and GRACE_PERIOD (e.g., 30 minutes). For longer locks, developers often favor block height over timestamps, as block height is less susceptible to manipulation by miners and provides a more reliable measure. Once timing is validated, encryption ensures that the voting process remains secure.
Encryption and Security Measures
Encryption is vital for keeping votes confidential until the time lock expires. Techniques like time-lock puzzles and Identity-Based Encryption ensure that decryption can only occur after the predetermined period.
Threshold decryption adds another layer of security by distributing cryptographic keys among multiple nodes, which only initiate decryption after the lock period ends. To prevent replay attacks, a unique "salt" value is included in each hash. This encryption also protects against Maximal Extractable Value (MEV) attacks by keeping transaction details hidden until they are included in a block, preventing adversaries from front-running or reordering votes. Combined with the automation of smart contracts and precise blockchain timing, these security measures form a robust framework for time-locked voting.
sbb-itb-8eb1bfa
Step-by-Step Guide to Implementing Time-Locked Voting
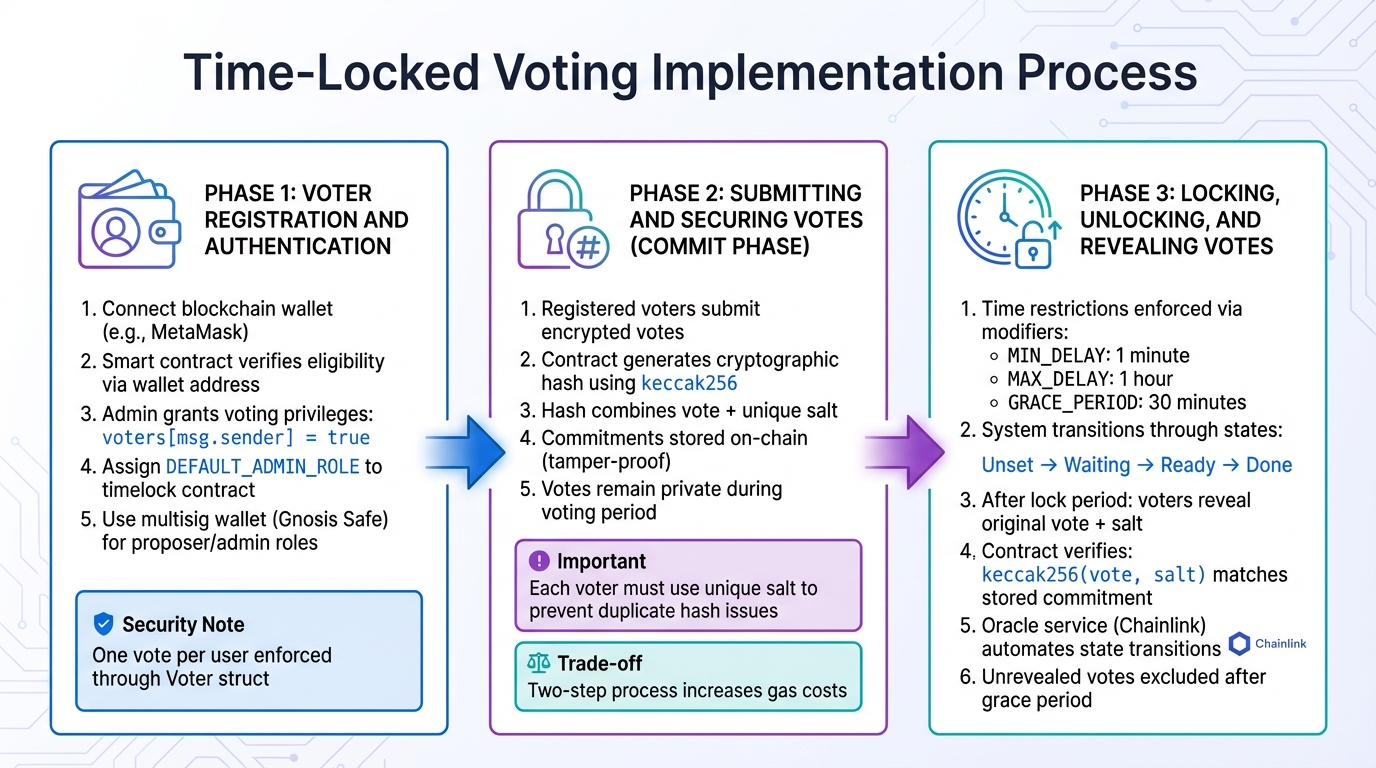
Time-Locked Voting Implementation Process: Registration, Submission, and Revelation Phases
Creating a time-locked voting system involves three critical phases: registration, submission, and revelation. Each phase ensures the process remains secure and transparent from start to finish.
Voter Registration and Authentication
To begin, voters connect their blockchain wallet (like MetaMask) for registration. A smart contract verifies eligibility by linking each wallet address to a Voter struct, ensuring one vote per user. An admin or chairperson grants voting privileges by setting voters[msg.sender] = true.
To reduce the risk of centralization, it's smart to assign the DEFAULT_ADMIN_ROLE to the timelock contract itself instead of a single wallet. Additionally, using a multisig wallet (e.g., Gnosis Safe) for proposer and admin roles can add an extra layer of security. Once registered, voters can move forward to secure their vote commitments.
Submitting and Securing Votes
In the commit phase, registered voters submit encrypted votes. The contract generates a cryptographic hash using keccak256, which combines the vote with a unique salt. This ensures votes remain private during the voting period. The commit-reveal model prevents voters from being influenced by earlier submissions.
It's crucial that each voter uses a unique salt. If two voters use the same salt and make the same choice, their hashes will match, which could result in only one vote being counted. These commitments are stored on-chain, creating a tamper-proof record. However, keep in mind that this two-step process (commit and reveal) increases gas costs. Once votes are committed, the focus shifts to managing the lock and reveal phases.
Locking, Unlocking, and Revealing Votes
Time restrictions are enforced through modifiers like onlyBefore(uint time) and onlyAfter(uint time). These ensure a minimum delay (e.g., 1 minute), a maximum delay (e.g., 1 hour), and a grace period (e.g., 30 minutes) for processing votes. The system transitions through four states: Unset, Waiting, Ready, and Done.
After the lock period ends, voters reveal their choices by submitting the original vote along with the salt. The contract verifies that keccak256(vote, salt) matches the stored commitment before counting the vote. To automate the transition from "Waiting" to "Ready", you can integrate an oracle service like Chainlink Automation. Any votes not revealed within the grace period are automatically excluded.
Applications of Time-Locked Voting for Communities and Events
Event Governance and Decision-Making
Time-locked voting brings a layer of transparency and security to managing community-led events. By requiring decisions to be publicized before execution, it ensures that changes - like reallocating funds, switching venues, or updating event rules - undergo a mandatory review period. Typically, this review window lasts between one and three days, giving community members a chance to assess and respond to proposals.
This approach relies on predefined roles to maintain balanced control. It prevents any single individual from steering the event unilaterally. If stakeholders disagree with a proposed decision, the delay provides them with an opportunity to withdraw their support or even leave the system entirely. This built-in pause not only encourages broader community participation but also aligns with the secure framework discussed earlier.
Standardized delay periods, a feature common in major DeFi protocols, play a vital role in preventing hasty or malicious actions. OpenZeppelin highlights the importance of such mechanisms:
"Timelocks are generally considered a strong indicator that a project is legitimate and demonstrates commitment to the project by project owners".
Integration with Platforms like Zenao.io
Platforms like Zenao.io, which specialize in decentralized event management, can adopt time-locked voting to enhance community governance for events such as festivals, workshops, and other activities. Using this system, stakeholders can vote on key details - like speaker lineups, budget allocations, or rule changes - with a transparent and secure process.
To ensure decentralized governance, the platform can use smart contract-based role assignments. For instance, ownership of the target contract should be transferred to the Timelock, while the Proposer role is assigned to a multisig wallet. This setup prevents any single organizer from making unilateral decisions. After configuration, the initial deployer should renounce their administrative rights, allowing the timelock to operate independently.
Additionally, external oracles can help automate voting windows, ensuring that votes open and close at precise times. This feature is particularly useful for coordinating decisions across different time zones during multi-day events. By integrating these mechanisms, platforms like Zenao.io can provide a secure and transparent governance structure for their communities.
Advantages and Limitations of Time-Locked Voting
Advantages Over Standard Voting Mechanisms
Time-locked voting introduces some notable benefits compared to traditional on-chain voting. One key improvement is the grace period it provides. Unlike standard mechanisms where decisions are implemented immediately, time-locked voting includes a delay, giving users time to adjust or exit their positions before changes take effect. This transforms governance into more of a negotiation, allowing stakeholders to maintain control over their involvement.
Another advantage is the prevention of impulsive decision-making. By enforcing a mandatory waiting period between the conclusion of a vote and its execution, this system encourages more thoughtful governance. As Elizaveta Timofeeva, a Backend/Infrastructure Software Engineer at Trezor, puts it:
"The waiting period adds a layer of security and careful consideration; it acts as an alert system by notifying parties before execution."
Time-locked voting also improves fairness by keeping vote counts hidden during the process. This prevents large holders from swaying results at the last minute and avoids discouraging smaller participants. Advanced implementations, such as those using homomorphic time-lock puzzles, eliminate the need for centralized tallying authorities. Results are revealed mathematically after the timer expires, which not only reduces reliance on intermediaries but also mitigates front-running attacks - where bots exploit advance knowledge of governance outcomes to gain an advantage.
Here’s a quick comparison of standard on-chain voting and time-locked voting:
| Feature | Standard On-Chain Voting | Time-Locked Voting |
|---|---|---|
| Execution Timing | Immediate upon vote conclusion | Delayed by a predefined buffer (e.g., 48 hours) |
| Tally Visibility | Publicly visible in real time | Hidden until voting ends |
| User Protection | Immediate outcome acceptance | Grace period for users to exit before execution |
| Trust Model | Often depends on tallying authorities | Can operate autonomously via cryptography |
| Front-Running Risk | High; bots can exploit visible pending trades | Low; transactions are encrypted or queued |
Challenges and Security Considerations
While time-locked voting offers several advantages, it also introduces technical and operational challenges. For starters, smart contracts, which are central to this mechanism, don’t have built-in timing functions. They rely on external oracles to manage voting windows, creating potential vulnerabilities.
Another hurdle is the cost of gas. Privacy-focused cryptographic measures, like Zero-Knowledge proofs or modular exponentiations, significantly increase gas fees on platforms such as Ethereum. To balance security and efficiency, some systems use 1,024-bit RSA moduli instead of the more secure 2,048-bit standard, reasoning that the data only needs to stay private until the vote concludes.
The delay itself can be both an asset and a drawback, especially during emergencies. For example, a one-day delay might be too short to allow proper intervention, which is why many protocols opt for a two-day minimum. To address this, some governance systems incorporate a "Pause Guardian", a role that can temporarily freeze critical operations like minting or borrowing while the delay period runs its course.
Privacy is another area where limitations emerge. Time-lock puzzles only provide temporary privacy - once the timer expires, anyone can decrypt individual ballots to see how users voted. Additionally, encryption methods like ElGamal can only handle smaller vote counts (up to roughly 4.3 million) due to computational constraints. These trade-offs require organizations to carefully evaluate their priorities around privacy, security, and scalability.
Conclusion and Key Takeaways
Summary of Core Principles
This guide outlined a structured approach to ensure secure, transparent, and deliberate decision-making within decentralized systems. A key feature is time-locked voting, which introduces a mandatory delay between a proposal's approval and its execution. This delay, as explained earlier, follows a specific lifecycle that includes distinct roles: Proposers, Cancellers, and Executors. Each role plays a part in maintaining a balanced and secure governance process.
The built-in buffer period - commonly set to two days for critical decisions - acts as both a warning system and a safeguard. This delay allows community members to review and discuss proposals, avoiding rash or impulsive actions. These principles form the backbone of governance methods for next-generation decentralized platforms.
Future Implications for Decentralized Systems
Looking ahead, decentralized systems are expected to adopt even more advanced practices to enhance privacy and autonomy. For instance, some emerging platforms are exploring homomorphic time-lock puzzles, which conceal vote tallies until the voting period ends, reducing the risk of undue influence by major stakeholders. Similarly, the use of Zero-Knowledge proofs could ensure long-term ballot privacy, offering communities a higher level of confidentiality in their decision-making processes.
For platforms like Zenao.io, these advancements open up new possibilities for democratic governance. Whether it's deciding on festival lineups, allocating budgets, or implementing policy changes, time-locked voting provides a crucial layer of trust and security. Additionally, the integration of oracle-based timing solutions - like Chainlink, which automates actions once delays expire - adds practical value to these mechanisms.
However, balancing security with ease of use remains a challenge. Past incidents highlight the importance of carefully calibrated delays and the need for robust emergency measures. As these systems evolve, time-locked voting is set to become a foundational feature across decentralized platforms, empowering communities to make decisions confidently while maintaining the safeguards necessary for secure governance.
FAQs
How long should a timelock delay be?
A timelock delay needs to be sufficient to give stakeholders enough time to review and react to pending transactions or proposals. Generally, this timeframe can vary from just a few hours to several days, depending on the system's governance requirements or security priorities.
What happens if no one triggers execution after the delay?
If the execution isn't triggered after the delay, the scheduled operation stays in a pending state, unable to move forward until someone takes action. That said, authorized users have the ability to cancel the operation, which resets its status back to "Unset."
How do you handle urgent emergencies with a timelock?
Emergencies that require immediate attention are handled either by bypassing the delay using an emergency mechanism or through an alternative process designed for quick access. Since standard timelocks are built to introduce delays, they aren't ideal for urgent, time-sensitive scenarios. Emergency protocols step in to ensure critical actions can be carried out without unnecessary delays when the situation demands it.
